ComplyDog Blog
A blog that helps software companies navigate GDPR compliance
A blog that helps software companies navigate GDPR compliance
Effective data security management involves creating systematic, holistic frameworks that protect information throughout its lifecycle, ensuring confidentiality, integrity, and compliance while addressing evolving threats and organizational challenges.
Posted by Kevin Yun | 2025-10-30T18:53:27.003Z
Learn what ROPA is, its role in GDPR compliance, key components, legal requirements, industry considerations, and how organizations can effectively manage processing records to ensure data protection.
Posted by Kevin Yun | 2025-10-30T18:49:14.819Z
GDPR data classification is essential for protecting personal information, ensuring compliance, and managing risks effectively through systematic categorization of data based on sensitivity and regulatory requirements.
Posted by Kevin Yun | 2025-10-29T19:00:40.303Z
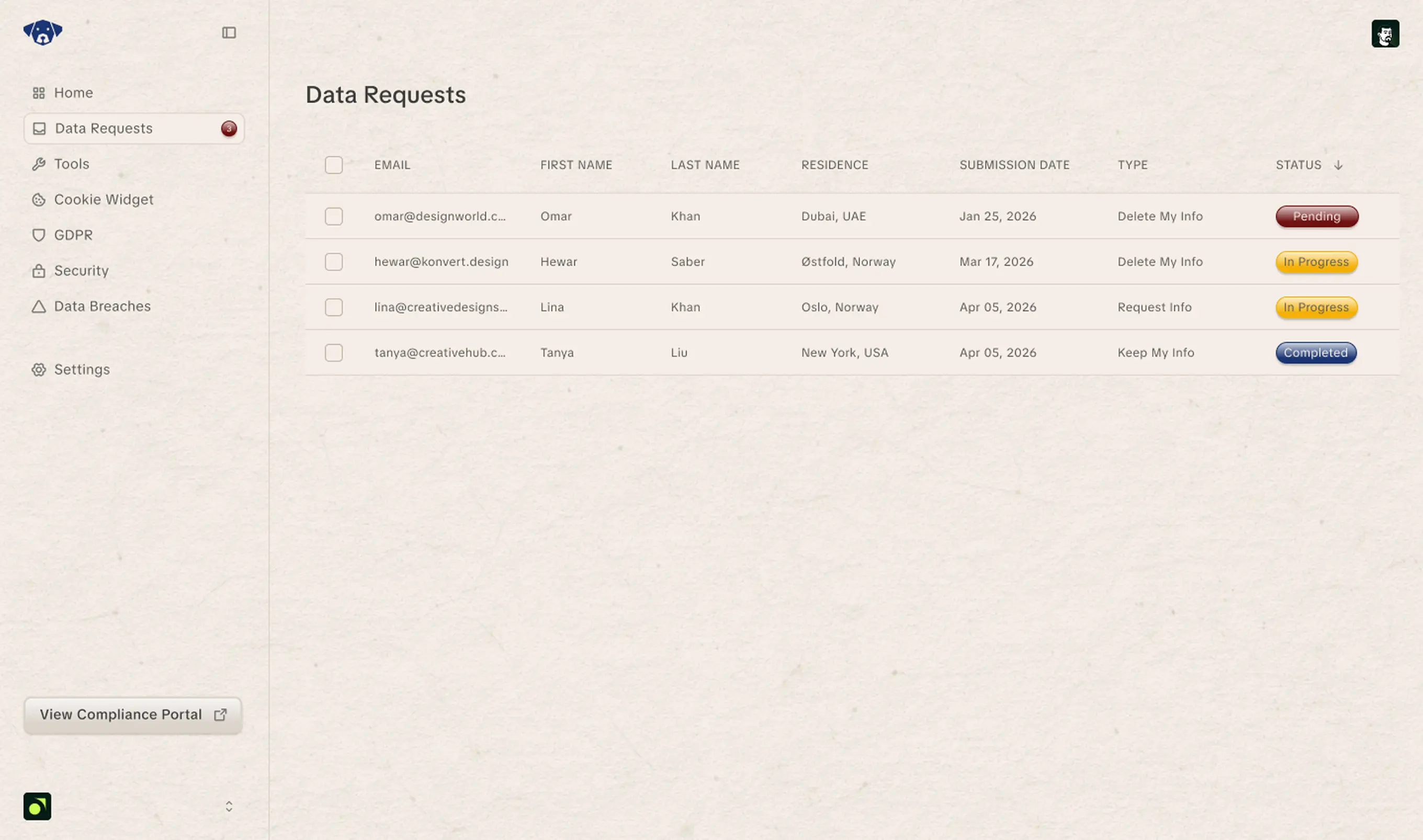
Learn how to effectively manage DSR requests, understand regulatory requirements, and implement technology solutions to ensure compliance, data privacy, and efficient handling of individual data rights.
Posted by Kevin Yun | 2025-10-29T18:55:22.446Z
Effective data governance rests on four pillars—data quality, stewardship, protection, and management—that create a reliable foundation for compliance, trust, and informed decision-making in modern organizations.
Posted by Kevin Yun | 2025-10-29T18:52:26.631Z
Sensitive data discovery is essential for identifying, locating, and protecting confidential information across digital environments, helping organizations prevent data breaches, ensure regulatory compliance, and strengthen security defenses.
Posted by Kevin Yun | 2025-10-28T18:51:50.285Z
Data Security Posture Management (DSPM) offers a data-centric approach to identify, classify, and protect sensitive information across multi-cloud environments, enhancing security, compliance, and risk mitigation in modern organizations.
Posted by Kevin Yun | 2025-10-28T18:46:03.871Z
Enterprise data encryption is essential for protecting sensitive business information, ensuring regulatory compliance, and preventing costly data breaches through robust, scalable, and integrated encryption strategies tailored for modern organizations.
Posted by Kevin Yun | 2025-10-28T18:41:57.241Z
Automate data privacy compliance with intelligent systems that continuously discover personal data, enforce policies, manage consent, and monitor risks—transforming reactive privacy management into proactive, scalable data protection across organizations.
Posted by Kevin Yun | 2025-10-27T15:41:27.221Z
Popular Posts
The 7 Basic Principles of GDPR Compliance
GDPR Cookie Consent (Banner): An Essential Guide, Checklist, and Examples

OpenAI's GDPR Compliance: Understanding the €15 Million Fine and What It Means for AI Companies
GDPR Software ROI: Is It Worth the Investment?
GDPR and the Consequences of Non-Compliance: What B2B SaaS Companies Need to Know
New to ComplyDog? Your Guide to Getting Started
What is a DPA? Data Processing Agreement for GDPR Explained
GDPR Compliance Checklist For B2B SaaS Companies
GDPR Implementation Examples: Success Stories for B2B SaaS Companies
With ComplyDog, our team was able to create a fully compliant GDPR page in just 30 minutes. We were impressed with how user-friendly the interface was, and how it guided us step-by-step through the process. The tool even helped us to identify potential privacy issues on our site that we hadn"t considered before, which was incredibly helpful.

Sagar Soni
Co-Founder at Requestify